If you asked me from September 2012 forward, the answer would change dramatically with WordPress Brute Force Attacks now exceeding 50% of all attacks being reported.
If you review your or your hosting provider reviews your web site’s access logs on a regular basis, you can tell if there are Brute Force attacks being attempted on your WordPress site by seeing multiple requests to access the file wp-login.php from the same IP address over and over again. Sometimes it might be a single request every x period of time; other times it might be scores of requests from the same IP address. By the way, are you or your provider regularly checking your web site access logs for abuse?
How can you protect yourself against WordPress Brute Force attacks?
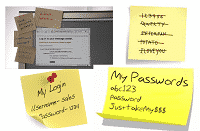
- Use strong passwords that are at least 12 wide which are unique to the user id and the application / device (you never re-use the same password for anything).
- Change your password every 90 days; and never re-use the same password from the past. Alternate the width of the password each time, never going less than 12 wide.
- Make sure your WordPress was installed in a secure manner. If your WordPress was installed by a hosting automation system rather than manually, the installation is insecure. Use the WordPress Hardening Codex to go through and harden your WordPress installation or ask your designer or hosting provider to do it for you.
- Go through the excellent check lists and articles at the WordPress Security Checklist site.
- If you can take advantage of limiting access to wp-config.php by IP address, then do so.
- Consider using plugins like More Security Login, Login Security Solution, and Limit Login Attempts.
- Consider using a hosting provider like our company that does review the logs for you, has intrusion systems in place to catch and stop most break in attempts, who does free daily backups and free restores who will work with you to keep your site secure.
Since nothing is hacker proof, should you find your WordPress site hacked, see our Site Security page for what we recommend for you to do (if you host with us, we do the clean up 100% in-house).
Do you have your own suggestions for how to protect against WordPress Brute Force Attacks? Let us know in the comment area below.
